When you track the results of your incident post-mortems to identify root causes of incidents, and when you conduct risk assessments to prospectively document vulnerabilities, you have the data to impress management on the consequences of failure to follow policy, procedures or other elements of your internal controls that contribute to risk exposure.
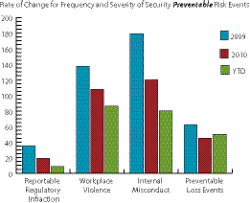
Objective: A significant percentage of security events are preventable. Use your metrics to influence behavior and fundamental corrective action.
Risk Management Strategy: In the example above, the CSO understands that it takes more than the open-ended “what if” to get management’s attention and obtain results. This security team knows that documenting “preventable losses” is likely to have far more impact than a spreadsheet full of incident statistics that may get lost in the roll-up of quarterly or annual risk reporting.
If you check in with your risk management group (the insurance side), you can have a fascinating discussion on fortuitous loss and preventable loss. The former are deemed unavoidable, owing to accident and chance, while the latter are avoidable and therefore, but for somebody’s misfeasance, malfeasance or nonfeasance, take away from the bottom line in more, shall we say, interesting ways.
When we conduct risk assessments that prospectively identify hazards and vulnerabilities that could be exploited by a knowledgeable insider or studious bad guy, we log an avoidable risk. Ditto for incident post-mortems that flesh out the root causes of security events.
Not all of these lessons uncover known exposures for which we have installed a countermeasure that has been breached or somehow failed. Discovering that which was previously unknown is, after all, the real gem in a risk assessment process. But this is about how to best use the unique knowledge you have on business process risk. This is about using that unique perch we have to see risk in ways that no other part of the business has.
This CSO understood that well-documented and reliable metrics can tell a powerful story and push results far more effectively than simply counting things and publishing spreadsheets that fail to inform and demand action. In 2008, he saw the risk of not sounding the alarm on risks he could prove were preventable. The trend was confirmed in 2009, and the decision to track several categories of risk events with this focus was affirmed. Four are displayed above.
• Reportable regulatory infractions run the gamut of consequences, but it’s the notion of “reportable” that makes this group of preventable findings potentially more severe. Avoidance of sanctions through compliance activities is the focus of significant internal controls and often significant expense. Failure has potentially considerable reputational risk.
• When its cause is admittedly preventable, a notable workplace violence event can have a devastating impact on victims and employees, not to mention a company’s psyche and bottom line.
• I could make a case that all internal misconduct is preventable if accountable people paid attention … but never mind. Think about market share, the value of trade secrets, reputation and how much the press loves stories about the well-placed insider gone bad.
• Preventable loss events are examples of internal controls not followed, managers not paying attention, good systems operated badly, low-bid vendors not effectively supervised, and top management not caring enough.
After spirited discussion, these four were selected by the CEO as requiring Board-level awareness and a commitment to targeted reductions. The results speak for themselves with significant reductions in three critical categories.
This is an example of how simple trending of data generated by a security organization committed to measuring program performance and proactive engagement with management can achieve an improved state of enterprise protection. Corporate Security here is a change agent capable of influencing corporate strategy while also increasing its visibility as a contributor to the company’s success.
George Campbell is emeritus faculty of the Security Executive Council (SEC) and former CSO of Fidelity Investments. His book, “Measures and Metrics in Corporate Security,” may be purchased through the SEC Web site. The SEC works with Tier 1 Security Leaders™ to reduce risk and add to corporate profitability in the process. A faculty of more than 100 security executives provides strategy, insight and proven practices. Through its pioneering approach of Collective Knowledge™, the SEC serves all aspects of the security community. To learn more, mail [email protected] or visit www.securityexecutivecouncil.com/?sc=std. The information in this article is copyrighted by the Security Executive Council and reprinted with permission. All rights reserved.
About the Author

George Campbell
George Campbell is emeritus faculty of the Security Executive Council and former CSO of Fidelity Investments. His book, “Measures and Metrics in Corporate Security,” may be purchased through the Security Executive Council Web site. The Security Executive Council is an innovative problem-solving research and services organization that works with Tier 1 Security Leaders™ to reduce risk and add to corporate profitability in the process. A faculty of more than 100 experienced security executives provides strategy, insight and proven practices that cannot be found anywhere else. Through its pioneering approach of Collective Knowledge™, the Council serves all aspects of the security community. To learn about becoming involved, e-mail [email protected] or visit www.securityexecutivecouncil.com/?sourceCode=std. The information in this article is copyrighted by the Security Executive Council and reprinted with permission. All rights reserved.