Physical security technology has advanced (and changed) considerably in the past 15 years. Yet, most end-users of security technology take the same approach to technology deployment that they did 15 years ago or more. If we want to advance the results we get from security technology (as opposed to simply getting the same results for lower cost), we will have to advance our thinking. This is the issue behind the following question from an end-user:
Q: At the ASIS Annual Seminar and Exhibits, I saw demonstrations of products that are compliant with the new PSIA and ONVIF interoperability standards. Since these products included the brands that I already use and plan to keep using, what actual benefit do the interoperability standards provide to me?
A: There are many values to be obtained from the adoption of interoperability standards, and most of these have been written about or analyzed in security industry trade journals, and online articles and blogs. However, to make sure that you benefit fully from standards adoption in the industry requires that you take a modern-day approach to security technology deployment. This can require a significant change in thinking ... one that includes the concept of "evolvable infrastructure."
Where Interoperability Standards Lead
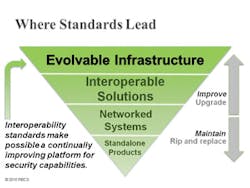
Wikipedia has an excellent article on the topic of "infrastructure," and many of the concepts relate to the benefits of establishing a security technology infrastructure. An evolvable technology infrastructure is the opposite of what has been the most common approach to security technology deployment, which was: purchase, maintain, then rip and replace. This was suitable when product lifecycles were 10 to 15 years long, and when the pace of technology advancement could be monitored easily by attending a trade show every four or five years. Now, technology advancements occur as frequently as every six months. Not only are annual rip-and-replace cycles not affordable, they are also not necessary to keep pace with technology advances.
Interoperability among networked devices means that it is now becoming possible to establish an infrastructure whose capabilities can be continually improved as technology advances occur.
The appropriate way approach security technology deployment is to establish an evolvable security technology infrastructure, defined as: A managed network of electronic security systems and devices that is configured, operated, maintained and continually enhanced to provide security functions and services that achieve specific security risk mitigation objectives.
The diagram to the right illustrates the evolution from standalone products and systems to achieving a standards-based evolvable infrastructure.
For a closer look at what the concept of an evolvable infrastructure means, view this online webinar: The Road to Interoperable IP Solutions (www.psialliance.org/PSIAWebinars.html).
One of the most important benefits to the adoption of interoperability standards is that it will make possible the continual improvement of security technology deployments so that security operations capabilities can evolve as business environments and risk profiles evolve.
If you have convergence experience you want to share, e-mail your comments to me at [email protected] or call me at 949-831-6788. We don't need to reveal your name or company name in the column. I look forward to hearing from you!About the Author

Ray Bernard, PSP, CHS-III
Ray Bernard, PSP, CHS-III, is the principal consultant for Ray Bernard Consulting Services (RBCS), a firm that provides security consulting services for public and private facilities (www.go-rbcs.com). In 2018 IFSEC Global listed Ray as #12 in the world’s top 30 Security Thought Leaders. He is the author of the Elsevier book Security Technology Convergence Insights available on Amazon. Ray has recently released an insightful downloadable eBook titled, Future-Ready Network Design for Physical Security Systems, available in English and Spanish.
Follow him on LinkedIn: www.linkedin.com/in/raybernard.
Follow him on Twitter: @RayBernardRBCS.