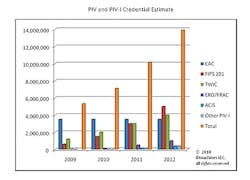
ID solutions will increasingly leverage PIV-I and its standards. Chart courtesy of IDMachines, LLC.
A roadmap of developments in access control progresses Identity, credentialing and access management to the top of the plan for enterprise solutions. Graphic courtesy of IDMachines, LLC.
There is a change taking place around identity and credentialing in the enterprise and government markets. Identity is now an enterprise business requirement with its own infrastructure, policy and budget. Identity makes use of open standards to achieve interoperability and requires the highest level of assurance. The change is that physical access control and other enterprise applications no longer issue credentials. Instead, they use a common digital identity of digital certificates and the 21st century utility of the Internet as well as private networks.
Physical access control is an application that authenticates individuals and devices and then authorizes administration, audit, access, surveillance, alarms, response, etc. for assets. Historically, facility and corporate security have issued badges for electronic physical access control. These have migrated over time from magnetic stripe to proximity to contactless. The introduction of smart cards for physical access control system allows multiple applications to store data or run on the cards. At the same time access control for networks, desktops, laptops and cell phones have continued to advance. User name and password management for the hundreds of applications in large enterprise has turned out to be a nightmare. Single sign-on does not address the underlying requirements for secure and efficient provisioning and de-provisioning. Mobile devices have become ubiquitous and wide area wireless networks are becoming commonplace. Add social networking on top of this and it makes the PACS scenario seem placid.
No wonder identity, credentialing and access management is at the top of the enterprise business agenda. Governance and regulatory compliance are business drivers whose needs are met by a strong identity, credentialing and access infrastructure.
All this led to the need for standards and policy for identity, credentialing and level of assurance. This is the same conclusion the Department of Defense came to 20 years ago and the reason they first implemented a smart card over a decade ago (1997). The U.S. Department of Commerce National Institute of Standards and Technology Federal Information Processing Standard (FIPS) 201 Personal Interoperability Verification (PIV) is used in over seven million credentials, growing to 14 million in two years.
The progression has gone from the Department of Defense, to Federal civilian government to all civilian contractors and now to other critical infrastructure and key resource sectors. In order to accommodate the non-government stakeholders and have others issue besides the Federal government, the PIV standard has an expanded framework known as Personal Identity Verification Interoperability or PIV-I. The PIV-I policy and framework recently reached maturity and has sufficient breadth to include devices (referred to as non-person entities).
Much of the growth in PIV-related credentials will be of the PIV-I policy. The defense industrial base, aerospace, transportation, education and bio-pharmaceutical industries have established cross-certification with the Federal government either directly or in more cases via industry bridges to issue these credentials. Utility, finance, state and local government will be the next sectors to follow suit.
In all of these cases FIPS 201 builds on the international standards for digital certificates. This standard is supported by Windows and Apple, Adobe and just about every major IT or mobile player. In fact, the Subscriber Identification Module (SIM) in phones use the same type of chip as a PIV-I credential. The same is true for National ID and National Health cards which are rapidly increasing in acceptance.
ID solutions will increasingly leverage the PIV-I framework and supporting standards. PIV-I provides the policy for sponsorship, enrollment, registration, issuance and activation as well as the technology to support it. Done correctly it provides a strong, interoperable and multi-use digital identity. This is no longer an option for government or the enterprise (whether they choose to leverage PIV-I or not) so the same is true for logical and physical access control.
Salvatore D'Agostino is a Certified Smart Card Industry Professional (CSCIP) and CEO of IDmachines LLC; www.idmachines.com and www.idmachines.blogspot.com.
About the Author
Salvatore D'Agostino
Salvatore D'Agostino
Salvatore D’Agostino is a Certified Smart Card Industry Professional (CSCIP) and CEO of IDmachines LLC