Centralized Monitoring and Investigations
With advancements in both networking and security technology and the cost of access to the Internet coming down, it has become more affordable to make centralized surveillance monitoring and investigations a reality. As the security industry continues to shift to IP, many believe that any IP-based system can be used to centralize these monitoring and investigation activities; however, this is a common misconception.
So, what functionalities should you look for when you purchase an IP system with remote operations in mind? Before we tackle this question, let’s first explore some scenarios and the associated benefits of centralizing your activities.
Remote Operations: The Benefits
Although having a security guard at each location may still be a necessity, a well-trained security team monitoring an entire organization can complement or replace this approach. Centralizing your security monitoring — especially after normal operating hours — can potentially increase efficiency and contribute to additional cost-savings.
Take the example of a bank that has branches worldwide and one global headquarters. A security system that provides access control as well as video surveillance is installed both at the branch level and at its headquarters. Protection is needed locally, so each branch has its own independent system. That being said, implementing a security system with remote operations enables monitoring of the local sites (the branches) in one central location (headquarters).
Both access control events and live and recorded video can be viewed from the central location. A central user can search for recorded video and access control events and alerts across all branches from one single location.
For example, all door forced open events for the entire organization can be found with a single search. Similarly, video associated to alarms from any branch can be retrieved and reviewed from headquarters in one easy search. Operators can even search all activities for a cardholder name and see all the branches he or she visited during the time period.
A city-wide surveillance application will also greatly benefit from the use of a centralized monitoring and investigation system. The police department may want to monitor cameras or access from specific sites such as an airport, government buildings and more. Live monitoring in this case will provide greater efficiency in response to emergency situations.
Different organizations, using the same system, could also share information for the benefit of greater security. In this case, the remote operation will offer more information to law enforcement agencies, while letting the local sites control what will be shared.
Both of these examples share distributed installation and configuration. If a local site is unavailable, central users will only lose connectivity to that site. If the WAN (wide area network) is not accessible, local users can still connect to the local sites independently.
Choosing The Right Platform
Given that remote systems tend to be more complex than your average security system installation, there are certain functionalities that one should look for. The following is a list that will help any organization make the right choice:
1. Multistreaming: This technology enables an IP video source to produce multiple video streams from the same camera at different levels of video quality. It can be used to optimize network usage on a WAN. Take a theft- or vandalism-related investigation taking place at the central site as an example. Unfortunately, bandwidth between sites is usually quite expensive and therefore limited. A remote security system should take advantage of multistreaming to record and view video locally at a higher quality, while transmitting a lower quality live stream to the central site.
2. Optimization of bandwidth: Bandwidth usage between sites will also become a problem in times of crisis when many remote operators require the same cameras at the same time. A remote security system that transmits multiple copies of the same stream over the WAN each time a single operator makes a request for the same stream is extremely inefficient — the load will be increased on the WAN and will slow down live video transmission. A well-designed security system will, on the other hand, understand the network topology and transmit video accordingly. In this case, only one stream per camera will be sent over the WAN, saving precious bandwidth to view as many cameras as possible. The streams will then be redirected to the central site into either multi-unicast streams or a multicast one, whichever is supported at the central site. This type of system will not let you down when you need it most.
3. Maps and visual tracking: No one can realistically expect remote operators to remember the position of cameras, doors, alarms and other entities across hundreds of remote sites. Therefore, opting for a remote security system with tools to help operators track people through a location or pull up video feeds quickly from any site will be very useful. Maps can graphically represent an organization’s workplace and can be an important tool when managing multiple locations.
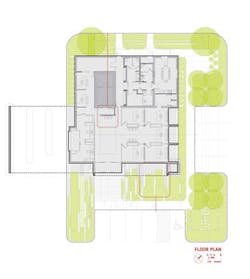
For example, a bank could have one map per branch displaying each floor plan with respective security entities (cameras, doors, alarms, etc.). Maps also provide various functionalities (view video from a camera, unlock a door, trigger an alarm, etc.) that help to group monitoring operations into one window. The graphical interface and elements of the entities are usually preferred by security personnel over a tree or folder-based structure like Windows Explorer.
Another useful operating feature is visual tracking. The cameras can be logically configured so a guard can retrieve the live stream of a camera based on its field of view. For example, a guard is monitoring the entrance door with camera A, when suddenly a man runs away to the right of the entrance door. The guard would just have to click on the right side of camera A’s video tile to switch the display to camera B, which would be displaying the area to the right of the entrance door.
Both these features will provide a system that is more intuitive, easier to navigate and requires less operator training.
4. Support for time zones: An incident is always reported in local time by the remote site operator; however, the central investigator often will not know the time zone of the different remote sites. The system should be able to manage time zones efficiently to provide the investigator with two different time search options.
Being able to search in local time removes the task of having to calculate the time at which the event took place at the remote site, or search based on the server time where the incident took place. It is therefore important to have a system that saves events in universal time (UTC) to be able to fulfill this requirement.
5. Installation and maintenance: The installation, configuration and maintenance of the entire system are also of great importance. An installation that can be started or scheduled from the central monitoring station is faster. A script that automates the installation on multiple servers concurrently can be created, hence speeding up the installation process.
Tools that allow for fast copying of the configuration will also be a big help. For example, a camera at a site is configured with the required video quality and motion detection settings. Those settings can then be copied to 50 or 100 cameras within the site, greatly speeding up the configuration process of large installations. There is no need to configure every single camera if the settings for all cameras are identical. Once a site has been properly configured, a lot of configuration options can be copied to other sites, again increasing the efficiency and reducing commissioning time.
Software upgrades can be especially troublesome if sites of different versions cannot communicate with each other. There is simply nothing worse than losing a connection to a site because of a version upgrade. For example, a local branch of the bank upgrades to version 4.5 of the security software which is not compatible with 4.4, the version installed at the headquarters.
In this case, the headquarters cannot monitor that specific branch until it upgrades to 4.5. But once at 4.5, the headquarters will not be able to monitor any of the other branches still running 4.4. A massive upgrade of all sites would be needed in that scenario, demanding more human resources and increasing the downtime of the system. Therefore, a system that provides forward and backward compatibility will alleviate the problem, allowing for versions 4.4 and 4.5 of a security system to communicate with each other. This ultimately provides a more gradual and streamlined upgrade path, and avoids any unnecessary downtime.