The reliability of our programs is an essential ingredient of executive confidence and support. If you are looking for a place to focus your quality assurance, shine it consistently on alarm system reliability and response. Whether they be experienced or uninitiated, customers find frequent invalid alarms unacceptable, and they make your responders distrust the validity of calls. When they occur at off-site facilities dependent on law enforcement response, false alarms often cost the company in fines.
Strategy: Anyone who has spent any time in a command center has heard the dispatched officer's radio response "checked area, negative results." The alarm came in from a point that deserved monitoring, but there was no apparent cause. If we assume the officer did his due diligence, what set of conditions contributed to alarm activation? On the dark side, an adversary may be testing response time and quality. On the maintenance side, that alarm point may be improperly installed or directed. On the risk assessment side, that alarm point may now be in an area where the activity, environmental or risk profile has changed and is impacting detection reliability.
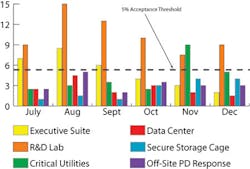
A large campus or a geographically distributed complex of facilities may have thousands of alarm points with disparate protection objectives. A prioritization scheme for this dispersed array is essential, and the simple chart above displays six focal points that may be found in a typical company.
In this example, we are tracking anomalies: six months of alarm events requiring a manned response resulting in no known cause. Our standard of alarm reliability is a 95-percent confidence level, so generally speaking, we are pretty good shape for this period of analysis. Depending on the value you attach to the assets being protected by this set of physical security elements, you may elect to increase or decrease this confidence level. But for some select portion of your alarm system configuration, it is essential that a standard of reliability and responsiveness be established and maintained.
It should be obvious to any security professional why we have elected to track the rate of nuisance alarms associated with executive spaces. Any of these may represent a significant area of risk exposure for the company. But as noted earlier, the most damaging impact of invalid alarms may be in the developed lack of confidence your first responders will have when that all-too-frequent address is dispatched. Security officer training should include procedures for checking alarm device operation, and alarm responses need to be appropriately documented in logs or incident reports to clearly indicate the validity of the alarm after an informed investigation of cause.
As for our fictitious facility in the example, we see an average of a 3-percent false alarm rate for facilities where no security presence is available. If you are fortunate enough to have police response available, that figure likely represents a frequency of fines from responding municipalities, or worse, notification that response will no longer be provided.
Nuisance alarms are measurable, and causes can be easily determined by qualified personnel. Alarm annunciation should be accompanied by the utmost degree of confidence that the activation is due to the risk for which it was installed and monitored. ?