A major shift has occurred in security technology development, and nothing in the security industry’s history to date has prepared practitioners to deal with it. Approaching today’s and tomorrow’s technology with yesterday’s thinking results in wasted money, wasted effort and an inadequate response to the changing risk picture. Especially in today’s economic and business climates, that’s an unacceptable situation for any company’s security function.
An informal survey of security practitioners about this article’s title — System Life Cycle Planning — found most practitioners asking how this differed from what they already do for annual maintenance planning. That difference — and it is major — is the subject of this article.
The shift in technology development is the result of digital computing, networking and communications technologies being incorporated into physical security systems, and new systems being developed based on technology capabilities that did not exist even five years ago. Some product life cycles are becoming as short as two years. New technologies are being developed every year and digital technology trends continue to shorten the pace of new product introductions. This accelerating trend, of which security technology is now a part, is depicted in the Technology Timeline.
To maintain effective security, security practitioners must radically alter their approaches to procuring and managing technology, starting now. It is not a matter of choice, unless the choice is to choose another profession, or to delegate technology planning and management.
Note the significant change in the Figure 1 timeline as of the year 2000. The Y2K projects of many companies included widespread upgrades and expansions to corporate networks, and the globalization of separated local area networks. This enabled a major acceleration of network-related technology development and adoption from this point on. Security technology advancement is part of this trend.
Warning
There is one caveat: this is not “just an IT thing.” It is not solely a matter of getting up to speed on IP-based technologies and networking. Effective deployment of security technology now requires:
• previous technical knowledge;
• previous risk and security operations knowledge;
• new IT technical knowledge;
• a deeper understanding of your organization’s security risk picture; and
• new perspectives, strategies and practices for technology planning and adoption.
The last two elements are new and must be obtained relative to the new technology shift.
Security, computer and network technology can do far more than they used to. But to obtain their beneficial use requires both a deeper understanding of the security risk picture of the business, and a technology approach that enables you to adapt your security technology to the risk picture on an ongoing basis.
The basic situation is that all technology is changing more rapidly. The world — and that includes business — is changing more rapidly as a result. This means that the security function has to be far more aware and adaptable that it has been in the past. New technology can help the security function in its advancement; thus, for practitioners, understanding the role of system life cycle planning is vital.
System life cycle planning is technology planning that takes into account the requirements for purchasing, installing, managing, operating and retiring products and systems throughout their useful life, as well as the technology value relative to current organizational needs and opportunities, and newer technology.
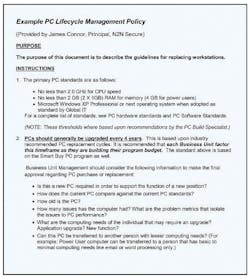
Research for this article found that some leading practitioners, who were more advanced in their implementations of digital security technology, had collaborated with IT and implemented life cycle planning according to existing IT standards. (See our example IT policy: Example PC Life Cycle Management Policy (PDF file)).
This is an excellent start as existing IT policies apply to many of the security technology elements — such as PCs, laptops and many network components. However, existing IT policies do not cover some of the security technology, and sometimes security needs will trump the IT policies and require what would otherwise be considered premature replacement. This happens when the technology must change for the improvement of risk mitigation — and therein lies a critical difference between IT systems life cycle planning and security systems life cycle planning. In the “old days,” security practitioners would often run every system or technology until its use could simply no longer be justified. Then, the system would be replaced wholesale. While that was appropriate for systems with 10- and 15-year technology cycles, it no longer fits today.
The Context for Life Cycle Planning
The purpose of IT systems life cycle planning is to optimize technology deployments for performance, efficiency and cost containment, including the costs of maintaining the networks and systems and even user training (total cost of ownership). This applies to businesses both large and small. (See 2006 IDC white paper: SMBs can Achieve Business Success Through IT Planning). However, security systems must be optimized for risk mitigation first and foremost, and secondarily for efficiency and cost containment (subject of course to overall budget restraints).
Because of this difference in purpose, it is important to think of deployed security technology as physical security systems infrastructure, rather than IT systems infrastructure, for reasons that will be made clear below.
Defining Infrastructure
Wikipedia has an excellent article on infrastructure. It explains that the word was imported from French, where it means subgrade, the native material underneath a constructed pavement or railway. The word is a combination of the Latin prefix “infra,” meaning “below” and “structure.” That definitely applies to terms like cabling infrastructure. Infrastructure also is used to mean the underlying framework of a system or organization. The term public infrastructure refers to the fundamental facilities and engineered systems serving a country, city or area, such as transportation systems, power generation and distribution systems, water supplies and schools.
Network infrastructure is the term for the underlying network cable and electronic components that support an organization’s information and communications systems. IT infrastructure can be used to refer to the total of computer, communications and network systems.
Thus, a physical security systems infrastructure is a managed network of electronic security systems and devices providing security functions and services in accordance with a risk management strategy.
Managed network is a term that conveys a world of meaning to IT personnel. While an in-depth definition goes beyond the scope of this particular article, it is accurate to say that a managed data network is well-planned and is maintained and enhanced (ideally behind the scenes) using the tools and devices needed to:
• monitor, report, analyze and diagnose the health and performance of the network to anticipate problems before they impact performance;
• maintain the network at user-required levels of performance; and
• expand and adjust its functionality and performance to serve the changing needs of its users.
The term infrastructure connotes an underlying framework for vital services important to a group or population (in this case the organization served by the security function). Thus, an infrastructure is considered an asset that is a strategic investment.
Wikipedia lists seven typical attributes of an infrastructure asset. I have revised and presented five of them below as being applicable to physical security systems infrastructures based upon new technology, especially enterprise-wide systems:
• The assets have a high initial cost and a value that is difficult to determine.
• They are a large systems network constructed over time and are not often replaced as a whole system.
• The systems network has a long life because its service capacity is maintained by continual refurbishment or replacement of components or subsystems as they wear out, become obsolete or require additional functionality.
• The system or network tends to evolve over time as it is continuously modified, improved, enlarged; and as various components and subsystems are re-built, decommissioned or adapted to other uses.
• The system interdependencies or new functional requirements may limit a component life to a lesser period than the expected life of the component itself.
Note that the concept of “high initial cost” is relative and changing. Due to technology advancements and cost trends, today $3,000 will buy more video storage capacity than $30,000 could have purchased 10 years ago. The above attributes are not generally applicable to the previous generation of security technology, but they are applicable to the networked systems of today and tomorrow — if we plan, design and manage them correctly.
Evolving Technology
In an evolving corporate network, fully functioning network switches are replaced (or upgraded) when the value offered by newer technology features warrants it. For example, many corporate networks have had their network switches and routers replaced or upgraded to provide Voice over IP (VoIP) capabilities, due to the tremendous cost savings involved (not for the network itself but for telephone communications) as well as for the additional features and integration available over traditional PBX phone service. VoIP switch and router functionality, in and of itself, adds no value to the network infrastructure; however, when used in conjunction with network telephones, it establishes a significantly higher ROI for the network infrastructure.
Similarly, the physical security systems infrastructures that we put in place now will, in the very near future, have perfectly working components replaced or upgraded to provide new functionality and integration capabilities that support improved risk mitigation.
Conversely, the integration and interoperability of new technology will allow some components to be used beyond their ordinary life or capacity. For example, it costs less money now to upgrade the storage capacity of DVRs whose hard drives are reaching their end of life (i.e. failing), using a common storage system known as an IP SAN (Storage Area Network), than it does to upgrade the individual drives themselves. Furthermore, it fixes the situation that some cameras have higher storage requirements than others — resulting in some DVRs having insufficient storage capacity, and some having too much — for the cameras that are connected to them. Shared common storage (which in large corporate information systems is called storage infrastructure), provides improved capabilities for less cost than the internal storage of individual DVRs.
The new generation of security systems and components are designed to function as part of an overall technology infrastructure. This requires that we change our thinking accordingly when planning, designing, maintaining and improving our security technology, to get the greatest financial and security ROI from our technology investments.
Infrastructure Perspective
Creating and managing a physical security systems infrastructure has impacts on all of the following:
• Technical assessment of existing technology;
• Financial assessment of existing technology;
• Strategic technology planning;
• Evaluation and selection of new technology;
• How any ROI case is developed — immediate and long term;
• Evaluation and selection of systems integrators;
• Partnering considerations with solution providers;
• Relationship with and support from the IT department;
• Skill and training requirements of security systems managers;
• Training requirements of security systems end-users; and
• Education of security program and project budget stakeholders.
It takes a little getting used to, but once you have adopted the infrastructure perspective, it is hard to go back to thinking about technology the “old way.” Infrastructure thinking is just part of the evolving subject known as “systems thinking,” which will be the subject of a future article.
Ray Bernard, PSP, CHS-III is the principal consultant for Ray Bernard Consulting Services (RBCS), a firm that provides security consulting services for public and private facilities (www.go-rbcs.com). Mr. Bernard has also provided pivotal strategic and technical advice in the security and building automation industries for more than 20 years. He is founder and publisher of “The Security Minute” 60-second newsletter (www.TheSecurityMinute.com).
About the Author

Ray Bernard, PSP, CHS-III
Ray Bernard, PSP, CHS-III, is the principal consultant for Ray Bernard Consulting Services (RBCS), a firm that provides security consulting services for public and private facilities (www.go-rbcs.com). In 2018 IFSEC Global listed Ray as #12 in the world’s top 30 Security Thought Leaders. He is the author of the Elsevier book Security Technology Convergence Insights available on Amazon. Ray has recently released an insightful downloadable eBook titled, Future-Ready Network Design for Physical Security Systems, available in English and Spanish.
Follow him on LinkedIn: www.linkedin.com/in/raybernard.
Follow him on Twitter: @RayBernardRBCS.