Metrics for Success: How Critical Is Cycle Time In Your Organization?
Objective: To examine security tasks to identify performance expectations and set specific objectives for delivery.
Business Focus: Business process management, Six Sigma, total quality management and continuous improvement are all terms we have heard in the frequent push and pull of corporate initiatives. Central to these themes is a focus on cycle time and how it can be reduced to improve productivity, cut cost and better serve the customer.
Setting cycle time targets for both internal teams and contracted service providers is an established expectation of the business. Security owns multiple processes that are labor-intensive within our own ranks, and they impact our customers’ time in multiple ways. Time, in a variety of parameters, is a key measure for our programs. Let’s look at a hypothetical case to see a few of the more obvious examples:
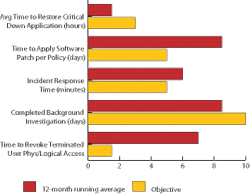
Critical Process Interruption: We all are aware of the implications of delayed restoration of a critical business process brought down by a security event. Contingency planning establishes a tolerance level for downtime, and plans are built to accommodate this level of risk exposure. In the 12-month period in the graphic, the time to restore the company’s designated critical applications was outstanding, beating the three-hour target by more than an hour.
Patch Management: Similarly, patch management tasks provide key performance indicators for information security administrators. Belated patch administration can seriously impact system reliability and availability. But patching is labor-intensive and potentially costly, and the diversity of systems in many companies only complicates this workload. Here, a five-day cycle time policy is being seriously exceeded, thus exposing the company to unacceptable risk.
Incident Response Time: I have frequently used this space to voice my concerns about incident response time and the circumstances that can impact this vital measure of life safety and security performance. While we can all agree that response time to an incident or call for service is an accepted measure for our first responders, what standard should be applied given the differing demands of business environments? How should we factor in the expanding delay time of off-site public safety services? This element of cycle time consideration is a headcount driver. Nevertheless, at least for a select set of risk events, response time is a key performance measure.
Background Investigations: New hire processes clearly impact business units, and Human Resource teams typically have established timeline targets for the hiring manager. Background vetting typically occurs toward the end of the process and can make or break a hiring decision. A 10-day target for the BI result seems to be typical, and here we see a running average of eight and a half days. Again, this can be a labor-intensive process involving multiple record searches and issue resolution, but hiring managers want to fill open requisitions ASAP.
Risk Avoidance Processes: In this example, we see a serious performance issue in the inability to meet the 1.5-day target to remove a terminated user’s logical and physical access authorization. Perhaps the more immediate problem for this company is allowing this amount of time for a disgruntled ex-employee to return potentially unchallenged to do some very serious damage. This metric provides the opportunity for a very engaged discussion with HR on how to reduce access revocation to minutes from termination rather than days.
Every task or element of work we conduct as part of our diverse security programs burns someone’s time — either ours or our customers’. As responsible managers, we must be assured that we are setting reasonably brief cycle times for our services and measuring conformance to these standards.
George Campbell is emeritus faculty of the Security Executive Council (SEC) and a former CSO. His book, “Measures and Metrics in Corporate Security,” may be purchased at the SEC Web site. The SEC works with security executives to provide strategy, and proven practices to reduce risk and add to corporate profitability. For more, mail [email protected] or visit
securityexecutivecouncil.com/?sc=std. This article is copyrighted by the SEC and reprinted with permission. All rights reserved.
About the Author

George Campbell
George Campbell is emeritus faculty of the Security Executive Council and former CSO of Fidelity Investments. His book, “Measures and Metrics in Corporate Security,” may be purchased through the Security Executive Council Web site. The Security Executive Council is an innovative problem-solving research and services organization that works with Tier 1 Security Leaders™ to reduce risk and add to corporate profitability in the process. A faculty of more than 100 experienced security executives provides strategy, insight and proven practices that cannot be found anywhere else. Through its pioneering approach of Collective Knowledge™, the Council serves all aspects of the security community. To learn about becoming involved, e-mail [email protected] or visit www.securityexecutivecouncil.com/?sourceCode=std. The information in this article is copyrighted by the Security Executive Council and reprinted with permission. All rights reserved.