Metrics for Success: Security's Metric Products
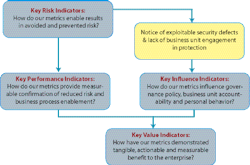
Our security programs serve specific clientele or management objectives in a variety of ways. Portrayed here are a linked set of essential indicators that should be an integral part of the security manager’s master plan and program measurement system.
An indicator is a sign, index or means to measure with accuracy. They can be portrayed visually with cues like meters or dials, or the stop, caution and go signals of a traffic light. Key performance indicators (KPI) are an integral part of business planning and strategy, as are key risk indicators (KRI) that guide enterprise risk management.
I have a bias about key performance indicators. I think in our business they must be tied to key risk indicators to tell the story about how well those risks are being managed by all the accountable parties. This notion of accountability is important. We are only a part of the protection equation and, although we may own the tool kit and a big piece of the rule book, enterprise protection lives or dies in attentive business processes.
I think it’s fair to say that a good KRI signals a clear indication of which direction a designated risk is headed. Have our control measures enabled risk avoidance? What results are we using to reach that conclusion? Is there a defensible line from the elimination of the exploitable security defect to a specifically directed security activity? Isn’t this the focus of our planning, and that positive result the key measure of this program’s performance?
What about influence? When we have accurately identified the risk exposure from proactive or reactive exercises, deployed the right countermeasures and effectively communicated responsibilities and awareness to employees and managers, we are using our unique pulpit to influence others who are part of the solution. Thus, our ability to influence results is a key performance indicator.
What about value? Proof of value can be elusive for us. It may be said that truly effective security is invisible, especially where it is effectively integrated into the daily business. Business executives understand the connection and the business rationale for an enterprise protection program, but they typically do not thoroughly understand what we do and why or how we do it.
It is a critical part of the security manager’s job to craft a message and educate top management on where and how we bring value to business strategy and the bottom line. This message has to include a variety of metrics that demonstrate our value story in business terms.
Is value found in avoided risk? Do we add value to business process when we enable it to do things that would otherwise be too risky? Here are a few examples:
- Digging to learn where the exploitable vulnerabilities lie.
- Making it difficult to hire and retain bad people.
- Providing for safe and secure places to work.
- Educating busy, inattentive and ignorant customers.
- Making life difficult for risky vendors and suppliers.
- Anticipating and planning for critical events.
- Providing flawless response when bad things hit the fan.
When we do a really solid job of building tangible measures of a program’s performance in mitigating risk or enabling a positive business result, our metrics become a centerpiece of Security’s value proposition.
George Campbell is emeritus faculty of the Security Executive Council (SEC) and a former CSO. His book, “Measures and Metrics in Corporate Security,” may be purchased from the SEC. The SEC works with security executives to provide strategy, and proven practices to reduce risk and add to corporate profitability. For more information, email [email protected] or visit
securityexecutivecouncil.com/?sc=std. This article is copyrighted by the SEC and reprinted with permission. All rights reserved.
About the Author

George Campbell
George Campbell is emeritus faculty of the Security Executive Council and former CSO of Fidelity Investments. His book, “Measures and Metrics in Corporate Security,” may be purchased through the Security Executive Council Web site. The Security Executive Council is an innovative problem-solving research and services organization that works with Tier 1 Security Leaders™ to reduce risk and add to corporate profitability in the process. A faculty of more than 100 experienced security executives provides strategy, insight and proven practices that cannot be found anywhere else. Through its pioneering approach of Collective Knowledge™, the Council serves all aspects of the security community. To learn about becoming involved, e-mail [email protected] or visit www.securityexecutivecouncil.com/?sourceCode=std. The information in this article is copyrighted by the Security Executive Council and reprinted with permission. All rights reserved.