End users see benefits of PSIM
As physical security information management (PSIM) software adoption continues to grow, public and private organizations are learning the many ways in which they can glean value from the technology that’s designed to convert real-time data into meaning, and actionable information from various security devices and systems to assess, analyze and enable more intelligent, effective and efficient management of unfolding situations. Here are a few ways organizations are using PSIM software to improve security, safety and business operations that would otherwise be impossible, extremely difficult, or costly without it.
Alarms
One way in which organizations use the software is to better understand the causes behind alarms – doors, fire, sensors, etc. - that go off throughout a typical work day. For one global Fortune 50 enterprise with PSIM software installed, when a door alarm sounds, video footage from the time and location of the alarm is immediately viewable. This enables security personnel to quickly assess the situation and determine whether action is necessary or not. For example, the operator may dispatch a security officer, allow the door to be automatically locked, and/or notify employees in the immediate area. Additionally, if an intruder is identified with the alarm, the PSIM software can track the movements of the individual making it easier for responders to quickly detain the person and identify whether or not that person is acting alone. Prior to installing the PSIM software, the standard alarm procedure was to send a guard to assess the location, often finding nothing due to the lag time between the alarm going off and the guard arriving at the site. While situations could be identified, it was difficult to know where a suspect came or went from without manually reviewing camera footage, a time consuming and costly process. PSIM software eliminates this manual review and, in the case of one enterprise organization, was able to reduce the number of false alarms being reviewed by 90 percent due to the automatic identification and accurate classification of false alarms.
Operator audits
PSIM software leverages a rules engine that analyzes data and policy information from multiple sources to correlate events, make decisions based upon event variables and initiate activities. Pre-packaged or user-written rules define the event or event combinations for identifying situations. The software also presents, in real time, instructions for resolving the situation based on standard operating procedures (SOPs). The software can then report and analyze the steps taken to resolve a situation and determine whether or not all the steps required for proper resolution were completed. These audits use to be manually performed, but with PSIM these reports are created seamlessly, tracking resolution steps for compliance and alerting organizations to any missed steps.
Organizations can also leverage PSIM software to monitor operator performance. One Fortune 500 company using PSIM software to improve its security practices knows it takes a particular amount of time for an operator to view video to visually verify an event before they can be certain they’ve seen the entire situation. If the operator closes the situation in less than the appropriate length of time, the situation is reopened and a manager is notified to review the resolution details. The manager can review all information pertaining to the situation to quickly understand the entirety of what happened and the response actions. This enables him or her to immediately address improper responses while optimizing overall standard response protocols. Prior to the implementation of PSIM, the security operating center supervisor spent one to four hours every day going through the last 24 hours of system responses looking for improper responses, such as multiple events closed in a very short period of time, each with the exact same explanation. The operator would review all system data separately and then manually piece it all together to understand what may have taken place.
Invalid card swipes
Numerous enterprises use PSIM software to automatically identify potential situations based on multiple invalid card swipes on a specific door within a defined time period. Operators are automatically presented with relevant video and card information to quickly validate whether or not the card holder and individual in the video match. Integration with an HR system provides the operator with seamless information as to whether or not the individual is an active employee. If not, action can be taken immediately. Prior to having the PSIM software in place, each system was looked at individually by different operators. The operators would then have to coordinate information and determine whether or not action was needed.
Unexpected events
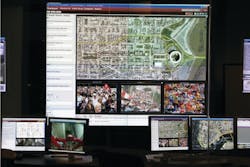
Prior to the City of Baltimore’s inaugural Grand Prix last year, its PSIM software was put through an impromptu test when the city experienced an earthquake and the remnants of a hurricane just one week before the race. The events proved to be the perfect catalyst to test the system, providing city officials with access to real-time information during the recovery effort. More specifically, it allowed the mayor to have a visual tour of the city, reviewing the live video feeds from helicopters so assessments and decisions related to impacted areas—specifically those without power—could be made. The city conducted real-time analysis of the natural disasters from one location with video, without needing to rely on radio communications - a capability that very few cities in the nation can claim. By having the PSIM software in place, the city was able to more rapidly and effectively respond to the situations resulting from the natural disasters.
Intellectual property (IP) protection
With PSIM, an organization is able to link RFID tags to ID cards. If an RFID tag alarms indicating property is outside of a building or secure area, the individual’s ID card tied to the RFID can be immediately viewed by a security operator and the owner’s location determined. This empowers security personnel to quickly and effectively respond to the potential IP breach. Prior to PSIM, the RFID tags and ID cards were managed in siloed systems, preventing data from being immediately correlated. As a result, the data had to be manually correlated, a time intensive process that would prevent security personnel from being able to take swift action.
Suspect identification and capture
After a distinguished U.S. university implemented PSIM software on its campus, its police were able to identify, track and retain five individuals involved in an attempted robbery on campus. Specifically, an officer saw a vehicle fleeing the scene and captured the license plate. PSIM software was used to verify the plate number, immediately pull up the video from the location and visually identify the suspects. As a direct result, four of the five suspects were criminally charged and the video evidence was used during the prosecution phase of the investigation. Without PSIM, the police would have spent hours after the incident sifting through video to identify the suspects, rather than taking swift action as the situation was unfolding.