When HIPAA (Health Insurance Portability and Accountability Act) was enacted in 1996, the fundamental objective was to enable portability of health records and coverage when someone changed insurance plans, and to reduce fraud and abuse. In order to achieve this, health information needed to go from being paper-based to an electronic format. It made sense since it is much easier to transmit and share information electronically.
This created a requirement to ensure that such data, termed “PHI” (Protected Health Information), is kept private and only accessed under authorized circumstances. HIPAA includes security and privacy as core components within the legislation, but the reality is that they are more of a byproduct rather than the primary objective. By design, it serves as high level guidance, yet stops short of prescribing what technology or implementation approach should be taken. In parallel, two federal agencies, the Office of the National Coordinator (ONC) and the Centers for Medicare & Medicaid Services (CMS) have been collaborating to define standards that will enable the secure exchange of health information across providers, payers (insurance companies) and patients.
We tend to think that our insurer already knows information about us, but their systems have been tuned more toward accepting and paying claims — often without the details on exactly what was done from a medical standpoint. In fact, most people have never seen their complete health record, and neither can their doctor.
Creating an ecosystem where Health Information Exchanges (HIE) can function without the reliance of direct point-to-point relationships is a focal point of healthcare IT strategy and planning. “There has been a great deal of progress, but the majority of healthcare entities are still concerned about controlling access to health information systems, applications and patient data,” explains Seonho Kim, Chief Architect at ApeniMED which specializes in enabling HIEs. “They require a stronger, standards-based, interoperable, and easy-to-use security infrastructure — especially federated identity and security and privacy controls. The result is that a lot of healthcare entities and systems still remain as silos. The lack of standardized strong identity would be the biggest obstacle in the success of health information exchanges and progressing toward next stages,” he adds.
The lack of standardized interoperable identity models in the healthcare IT environment has created a huge gap in operational efficiency, cost and quality of care.
Defining the Stakeholders
There are obvious non-technical challenges that each primary stakeholder group faces in the healthcare environment:
- Patients need to know they can receive and afford the best-quality care and it will be paid for, in most cases, by their insurance provider;
- Healthcare providers must be assured that the insurance companies will pay them, that they have the ability to perform the best in timely care at the lowest possible cost, with the ability to track fraud and abuse of the system; and
- Insurance providers and the government (Medicare/Medicaid) need insight into aligability, outcomes verses cost, detect and track fraud before offering payment.
These concepts form the framework for how identity and security can play a role in meeting all three stakeholders’ needs. Without a federated patient identity, healthcare providers and insurance companies cannot get a full picture of a patient’s medical information. Having a full view of the latest medical information for patients is critical — beyond the obvious quality of care, it can also reduce the registration process and administrative workflows, thus reducing costs for all stakeholders.
Dealing with Fraud
A common theme of fraud is found among all public- and private-sector stakeholders — but especially in its relation to Medicare claims. The current model is often referred to as “pay and chase” because the typical procedure for the government is to pay a bill and see if an anomaly turns up later. The tools for spotting anomalies are very poor and because they happen on such a large scale, keeping pace becomes a losing battle.
Criminals have figured out how bad it is. They can buy lists of stolen patient identities off the black market, steal or forge a doctor’s prescription pad, and start billing as much as they can in fake procedures, prescriptions and equipment. This goes on for a month or two since, for example, Medicare’s policy is to pay within 15 to 30 days of any claim. After racking up millions of dollars in fraudulent income and by the time an investigator arrives, the criminals are long gone and an empty shell is all that remains.
Fraud on this type of scale is alarmingly easy and low-risk. All a criminal needs to execute fake claims are four pieces of patient information, such as name, social security number, address, date of birth, and of course know that the stolen identity is legitimately covered under the Medicare program.
How big is the problem? In 2012, a RAND Corp. analyst and former CMS administrator estimated that fraud and abuse cost Medicare and Medicaid as much as $98 billion in 2011. There has been talk of hiring more investigators to attempt to curb the losses; however, it would make more sense to invest in transforming the legacy paper-based identification model to align with the electronic medical record model we have already chosen. If done correctly, it would decimate fraud incidents before they happen, have a much stronger digital trail for the few that do, and get a grasp on metrics that help correlate information at the time of care — when it really matters.
Stronger Identity means Stronger Cards and Protection
A digitally trusted identity ecosystem for federating medical data can be leveraged to issue identification cards that are more secure, smarter and useful. As we all know, patients and plan beneficiaries are already issued cards — flimsy paper or plastic things that display static data that could be used for fraudulent activity and don’t serve much other purpose. In the technical evolutionary scale, they are on par with identification that was issued in the 1950s.
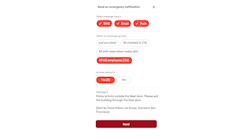
By leveraging a smart card that has a purpose-built secure microprocessor chip, it can prevent displaying static information to unauthorized persons, while holding the patient’s latest CCD (Continuity of Care Document) and optional data. This would empower providers to have access to allergies, history, procedures, immunizations, and so on, even if their system is not connected to an HIE or the patient is not conscious.
This means instant accurate information — right when it is needed without going through paperwork, phone calls and being a detective before applying care. A CISO of a state Medicaid agency recently told me that he is looking at smart cards as a portable DR (disaster recovery) platform to deal with emergency scenarios where paper records are otherwise not accessible or gone entirely.
The stronger cards could also be applied to the healthcare workers themselves. Doctors and administrators would be able to securely identify themselves while performing procedures at the time of treatment to eliminate “phantom” and excessive billing. The DEA already requires strong authentication procedures for Electronically Prescribed Controlled Substances (EPCS), and these smart cards could be a perfect fit. The federal government already has mature identity, security and other identification standards such as FIPS 201; however, these standards would need to be modified to suit the needs of the healthcare industry.
The digital evolution can also play a role here, as the smart authentication already exists in most smartphones. Other form factors are also possible — including watches, inpatient bracelets and others.
Barriers to Adoption
While all the above makes perfect sense, there are still barriers to immediately implementing a federated healthcare identity system. Here are a few of the challenges:
Lack of standards: While standards exist in many aspects within healthcare, is it almost void for the issuance, usage and acceptance of identity — especially in the context of going between separate organizations. Without this, organizations that use current technology to solve near-term challenges could be in jeopardy of being out of compliance in the future; thus, creating a much higher cost. A big part of the success will hinge on the evolution of standards that will enable reusing previously issued identities rather than creating them all over again. There is important work going on here, but it needs more time and evolution.
Mobile technologies: Unfortunately standards relating to the distribution and usage of identity credentials within mobile technologies are not yet mature. A new standard should incorporate a mobile roadmap to incorporate over-the-air transmission of credentials to mobile devices as an efficient and secure alternative to issuing cards.
Recommendations & Best Practice
For those healthcare organizations intent on moving forward with a federated identity plan in lieu of full standards development, here are some recommendations:
- Sponsorship is critical: Ensure high level support from your executive stakeholders.
- Form a cross functional stakeholder team consisting of domain expertise outside of IT (claims, etc).
- Build requirements by first understanding what problem is being solved.
- Determine the LOA (Level of Assurance) required for users, relying parties and stakeholders.
- Consider how workflows will be enabled or impacted — user adoption or mutiny depends on it.
- Other countries: Consider what they have done but realize the U.S. has a different model.
- Interact with vendors. Don’t just issue RFPs — vendors can help you innovate and provide insight.
- Filter out vendors that pitch generic products rather than a healthcare solution.
- Develop a risk matrix for long term viability and risks associated with each option. Estimate the full impact.
The healthcare industry — both private and public sectors — needs to come together and bring identity and security to the forefront at the boardroom level. When both sides of the table share the same vision and work together to achieve it, security and identity will transform from being viewed as a cost center to a significant business enablement platform in an industry and needs it most.
Terry Gold is Founder of IDanalyst, a vendor-neutral research and advisory firm focused on security, identity and privacy. He is an expert in advanced authentication, digital identity and services over connected devices and has developed core methodologies that assist corporate clients and investors simplify complex technology initiatives and investments. To read a longer white paper-version of this article, please visit www.idanalyst.com/healthcareid.