The proliferation of smartphones and tablet computers has created a dilemma for security managers: How do you enable your workers to maximize their productivity while at the same time providing adequate protection against data breaches?
There have been an ever increasing number of studies conducted on the topic of employees using their own mobile devices for business use and the conclusion that can be drawn from most of them is that if you are going to allow employees to use personal devices in the workplace, then you need to have written policies and guidelines in place detailing what company data they can access and share via those devices.
According to a survey of 500 business and IT professionals conducted earlier this year by CompTIA, a non-profit trade association for the IT community, only 22 percent of companies were found to have such a formal policy in place. Twenty percent of respondents said that their organizations were in the process of building policies at the time of the survey.
Yet another survey released this week by web security solutions provider Blue Coat Systems found that businesses are not realizing the full productivity potential of mobility out of fears and uncertainty over malware and putting security controls on a worker’s personally owned mobile device. The "Blue Coat Mobility Study," which polled 350 respondents, examined the different perspectives between IT departments and regular employees when it comes to bring-your-own-device (BYOD) policies.
According to the study, most IT departments (83 percent) said that they allowed workers to access corporate email accounts via their own mobile devices. Another 56 percent of IT respondents said that they allowed employees access to instant messaging on their phones. However, IT personnel were much less inclined to allow workers access to the organization’s ERP, sales force automation and supply chain management applications.
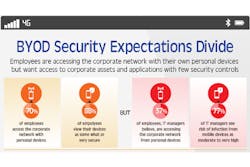
While IT staff may be leery what employees should be able to access on their smartphone or tablet, the view of regular workers is much different when it comes to what people are actually doing with their personal mobile devices. More than 70 percent of employees reported accessing the company network with a personal device; however, only 37 percent of IT believes that workers are doing so. A majority of employees (88 percent) also believe that their mobile device is secure, compared with just a fraction of IT workers (22 percent) who that feel they are. And then there is the quandary of exactly what security controls should be in place on employee-owned devices being used in the workplace.
The reality is that there is not a one-size fits all approach when it comes to regulating BYOD. Every organization is different and there are number of different factors that have to be taken into consideration. First and foremost, you have to decide which employees will be allowed access, as well as the types of devices you are going to support as each smartphone and tablet comes with its own set of vulnerabilities. Information security experts warn against allowing any and all devices to have access to the network.
Five tips recommended by Blue Coat to securely enable BYOD include:
- Securing the corporate network
- Extending malware protection to mobile devices
- Closing security gaps in mobile applications
- Setting contextually aware policies
- Using real-time reporting data to quickly identify and fix infected devices
The bottom line is you have to craft a policy that fits the needs of your organization. Don’t assume that just because you have a company policy governing the use of company-owned computers that it will carry over to workers accessing the corporate network with their own devices. As with any other guidelines, your BYOD policy needs to explicitly detail what is and is not acceptable.
About the Author
Joel Griffin
Editor-in-Chief, SecurityInfoWatch.com
Joel Griffin is the Editor-in-Chief of SecurityInfoWatch.com, a business-to-business news website published by Endeavor Business Media that covers all aspects of the physical security industry. Joel has covered the security industry since May 2008 when he first joined the site as assistant editor. Prior to SecurityInfoWatch, Joel worked as a staff reporter for two years at the Newton Citizen, a daily newspaper located in the suburban Atlanta city of Covington, Ga.