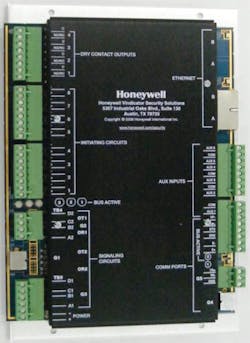
UHS-1500 device
Honeywell has released the UHS-1500 device for its Vindicator V5 access control and intrusion detection systems, which are primarily used to protect government and military installations. The device features dual Ethernet ports that provide physical and logical redundancy, a critical capability for end-users who must protect mission-critical facilities from the increasing threat of cyber attacks. In addition to dual Ethernet ports, the device uses advanced cryptography to reduce the threat of data being captured or compromised. To secure communications between field devices and the system's controller, the unit can use either TDEA encryption or the new AES encryption that was recently implemented by the Department of Defense to meet heightened encryption requirements.