When you wake up in the morning, turn on the light, switch on the television and start the coffee maker, your thoughts are likely on the day ahead and not whether you have enough capacity to power these items. You're free of these worries because the power company has created a reliable service, shared among the community, that scales to your individual, immediate demands. Since the service is metered and based on use, you pay only for your fair share.
The basic concept behind cloud computing is similar. Many companies are creating cloud services in a "pay as you go" scenario. These include sharing networks, computers, storage and even software applications.
Software as a Service, or SaaS, is the moniker for software applications delivered via the Internet from companies such as: Amazon, IBM, Salesforce.com, Microsoft, Google and others. SaaS is contrasted with the traditional "shrink wrapped" model for application delivery where the user installs and configures the software on a machine they own and maintain.
Growth trends for SaaS are strong: Gartner Inc. predicts the SaaS market will continue to grow more than 22 percent per year and that by 2011, 25 percent or more of new software systems will be delivered as SaaS applications.
So why is SaaS emerging as the dominant computing model today? The answer is the way in which the technology addresses the key needs and concerns of consumers, or what we call "the 5 C's:" Change, compliance, cost, continuity and coverage.
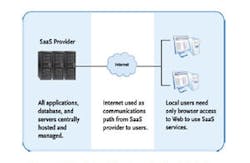
SaaS providers create multi-tenant software hosted in the cloud with the following basic attributes: All applications, databases and servers are hosted on the service provider's own infrastructure, typically at sophisticated outsourced data centers;
The public Internet is used as the communication path from the SaaS provider to users, with appropriate security measures in place;
Local users require no dedicated PCs or software applications, but gain access to the resources they need from a range of Internet-connected devices.
In the physical security world, the client/server model for delivery of applications has dominated most complex applications while an early precursor for SaaS, namely central station alarm monitoring, has dominated the less complex applications. Alarm monitoring is essentially a model for efficiently delivering pooled central resources to a group of users. The infrastructure, computers and personnel in today's central stations are shared among a group of clients. Each client pays a small fraction of the cost they would bear if they had their own dedicated central station.
Security as a Service takes the central station model to a new level, providing unprecedented end-user control over system functions while preserving complete segregation of data. Leveraging multi-tenant software and efficient hosting environments, SaaS for security drives costs down and service levels up.
Physical and logical security are among the top priorities for most organizations today. Having a sound risk management plan for security is as basic as having a sales and financial strategy. To understand the potential impact of Security as a Service, we will explore in depth the 5 C's, or the five areas of strategic importance for all organizations.
1. Change
Organizations face a constantly changing array of pressures-competitive threats, new regulations, financial uncertainty, technological shifts and business risk all force managers to maintain a state of perpetual vigilance. Savvy managers are building lithe organizations with systems and infrastructure capable of responding to threats and capitalizing on opportunities with amazing speed. Today's CEOs look to their CIOs and CSOs for answers on how to be more competitive, not simply to deliver a service.
The SaaS delivery model supports these objectives by providing capabilities that can be rapidly deployed and retracted based on fast-changing needs. In the context of physical security, SaaS applications allow CSOs to provision new security capabilities without investing in the technology and human resources required to support the service. Also, since the SaaS model is built around ever-improving technology supported by monthly fees, CSOs can ensure access to the latest features without worrying about upgrade patches and hardware limitations.
2. Compliance
Corporate governance, risk management and compliance with policies and regulations are in sharp focus for most organizations. It's not enough to express intent to follow regulations and policies, organizations must measure and transparently report on how completely they are complying.
In the context of physical security, compliance failures can result in data breeches, exposure to financial losses, denial of service attacks, and bodily injury to employees and visitors. The use of traditional physical security client/server architecture exposes company assets and personal information to constant threats. A typical corporate installation may include dozens of PCs, each with access to security controls and sensitive personal information.
SaaS architecture greatly simplifies enforcement of compliance polices and audits by providing centralized capabilities to establish standards as well as tools to track and report on compliance. Since a SaaS solution database is centralized, the cost for performing compliance audits is significantly reduced. Many SaaS providers provide evidence of internal controls certified by independent auditors, eliminating the need for a subscriber to incur these costs.
3. Cost
The survival of every organization hinges on its ability to deliver value to its customers. Referring back to the power example, what would it cost each of us to install and maintain a personal power plant? While it seems obvious that a personal power plant doesn't make sense, most physical security applications are delivered in this way. Software and hardware are purchased with sufficient capacity to handle present and some future needs. The equipment is installed, powered and maintained with internal resources. Often, excess resources exist in the host computers and within each machine that is operating the client software. When you add up the total cost of ownership, you will likely be very surprised.
The SaaS-based Security as a Service model provides an excellent alternative to the traditional options, thus allowing organizations to focus on their core business. SaaS delivers outstanding economic value for the following reasons:
- All users share and benefit from a common computing infrastructure.
- The cost model is scalable with users only paying for what they actually consume.
- Consumers of an application are free of all "back-end" management and maintenance expenses.
- Up-front capital expenditures are replaced with flat, subscription-based operational expenses.
Beyond the excessive capital outlays for traditional options, recent studies have established that the largest portion of application and server ownership costs actually exist in ongoing operational expenses, maintenance and support agreements. This is particularly true of computer systems that provide infrastructure services like security, because they must be held to a higher standard of availability and performance than ordinary office equipment.
In the case of physical security for a typical branch office or managed property scenario, the SaaS model for security management offers significant operational and financial savings due to both upfront cost reductions and the economies of scale of hosted application services.
4. Continuity
It's not enough to ask how much back-up protection exists, but also how fast can we resume operations if everything goes wrong? Organizations routinely spend hundreds of thousands of dollars on hotstandby computers, back-up power sources and disaster recovery locations for their physical security platforms. These measures are not only expensive; they often rely on internal computer networks that are likely to be challenged by any form of massive disaster. While security is certainly a high priority, if an organization's core revenue generating capabilities are down, what will be addressed first?
Fortunately, the SaaS model provides numerous answers for these types of challenges. Multi-tenant SaaS services are normally hosted in highly reliable data centers with built-in redundancy. The best providers also employ separate disaster recovery centers to restore full operations if the primary center is disabled. Redundancy in the communication path is built into this model due to the Internet's capability to send information via numerous routes. Even if broadband service is down, it's possible to establish the same communication paths via cellular cards and cellular equipped access panels. Since no special computers or software are required to operate a SaaS-based physical security application, any computer connected to the Internet can be placed into service during an emergency.
5. Coverage
Organizations often find the best way to accelerate profitable growth through geographic expansion. Expansion comes with significant challenges, risks and expenses. Security as a Service solutions provide clear benefits for organizations with geographically dispersed sites. The low initial costs and wide scalability of SaaS solutions give organizations access to world-class technologies with an economic model that promotes expansion rather than restricting it. Securely using the public Internet as a communication medium greatly simplifies the deployment of remote sites for IT departments. Even better, the centrally hosted SaaS model provides all the central oversight and management necessary in well-run organizations without requiring costly investments in a dedicated infrastructure.
A SaaS-based security platform gives you the power to drop an access control point anywhere in the world and have it communicating, configured and controlling your facility in a matter of hours, with complete synchronization to your master database and with total audit capability from wherever you happen to be. With the complexity of local software and hardware configurations removed from the equation, installers with even modest training can successfully implement a SaaS-based physical access control solution.
SaaS changes our relationship with software by allowing us to focus on what it does for us rather than the infrastructure required to make it work. It also changes our relationships with software providers by creating a mutually dependent environment in which the service seller is fully committed to the customer's outcomes. A customer simply will not continue to pay for a solution that does not provide ongoing value to their organization. Organizations best served by rapid access to state-of-the-art technology offering tremendous scalability and predictable costs over time should consider a SaaS-based option for physical security.