Ransomware: The Risk is Real
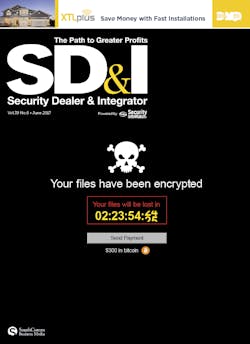
On May 12, the now-familiar threat of ransomware took the offensive, as more than 230,000 computers in 150 countries were encrypted for ransom at hospitals, telecommunications systems, governments, banks and more. Known as “WannaCry,” the ransomware demanded 300 bitcoin in exchange for decryption.
The attack exploited known vulnerabilities in an older version of Microsoft Windows – vulnerabilities that could have been avoided with recent patches. Worse yet, the global cyber-attack may be only the first in a series of sophisticated attacks that may arise out of leaked NSA hacking tools.
Britain’s National Health Service was hit by the cyber-attack, which encrypted and locked up data, resulting in the need to turn away patients and cancelling surgeries and other operations, causing what is still undetermined monetary loss and business continuity. The attacks continued to grow as the same attackers froze computers at Russia’s Interior Ministry while further affecting tens of thousands of computers elsewhere. Across Asia, several universities and organizations reportedly fell prey. Renault, the European automaker, said its French operations were one of the casualties, while its plant in Slovakia ceased operation because of the digital scourge. The attacks spread quickly to more than 74 countries, with Russia worst hit and included Ukraine, India, Taiwan, Latin America and Africa.
Cyber threats and ransomware in particular is one of the most talked about topics among the security community today. Ransomware presents a major threat across all businesses and vertical markets. Much of the ransomware is coming from out-of-country hackers who are quite adept in their attacks, often demanding bitcoin as payment.
“Ransomware is arguably the No. 1 method of cyber-attack in 2017, and this attack demonstrates the paramount need for critical enterprises to have a ransomware playbook in place for when they are attacked,” says Rich Barger, Director of Cyber Research for Splunk.
Adds Jonathan Sander, Chief Technology Officer for STEALTHbits Technologies: “WannaCry does nothing original – it is a Frankenstein's monster of vulnerabilities with patches and exploits that were stolen from the NSA and published for all to see. The reason for WannaCry's success is our collective failure to do the basic security blocking and tackling of patches, user education, and consistent backups.”
Online extortion had a banner year in 2016, according to Trend Micro’s annual security assessment report: “2016 Security Roundup: A Record Year for Enterprise Threats.” In 2016 there was a 752 percent increase in new ransomware families, with $1 billion losses to enterprises worldwide. Experts at the University of Maryland's Robert H. Smith School of Business say the WannaCry attack's real impact might be yet to come; in fact, they predict the assault could mark a turning point in the way institutions handle cybersecurity.
Most security experts do not recommend supporting these terror organizations by paying them, as it leads to further risk of additional attacks and promotes the criminal mindset of the ransomware industry. But the fact is, without appropriate data backups, organizations are left with little choice.
Ransomware attacks are growing in frequency, causing devastating consequences to enterprises and organizations across the globe. Numerous, widespread breaches around the world occurred prior to WannaCry, but the event has served as another wake-up call to the end-user community across the globe.
But what does this mean for security integrators and their role in creating a viable, proactive plan and strategy to combat ransomware for clients?
The Physical Security Target
Are physical security systems now emerging as a major target of ransomware attacks? The stark truth is that anything riding on the network is at risk. Physical security systems are vitally important to daily operations of every organization.
At many facilities, any downtime of these systems may significantly affect the safety of people, property and assets. As an example, mass notification systems are widely used to communicate emergency information to students, staff and visitors across a campus. They deliver messaging during active shooter situations, lockdowns and potentially deadly weather phenomena – and communications must reach recipients quickly and successfully. If ransomware was to wreak havoc on critical communications like mass notification, users would not be able to send or receive information or instructions, putting them at significant risk.
In Jan. 2017 in Washington D.C. – just prior to the presidential inauguration – hackers were able to leverage ransomware to take over 70 percent of the network video recorders (NVRs) run by the city, leaving them unable to record video surveillance for days. Reportedly, engineers were able to go to each location and conduct a system wipe and re-install rather than handing over the ransom. The event illustrates ransomware’s potential enterprise-wide catastrophic effect and lengthy remediation period that follows.
Many organizations rely on video surveillance systems to meet compliance rules and regulations, which often requires archiving a minimum of 90 days or more of recorded surveillance streams. As I have personally witnessed during numerous project deployments, system integrators are simply installing NVR appliances on-premises, with no database or video recording backup. This places the end-user at significant risk if a ransomware attack were to take place – the data would be lost and more than likely the only way to potentially have it returned would be through payment.
The Impact on Your Customers
As systems integrators, we owe it to our customers to be able to take physical security systems to the next level and provide the most current trending safeguards possible. Security integrators are the experts end-users turn to for advice and tactics to prevent cyber threats, ransomware and other malicious attempts on physical security systems which may be used circumvent the network or access customer data.
If you work in the healthcare market, this is even more critical and subject to numerous rules, standards and regulations – including the Health Insurance Portability and Accountability Act of 1996 (HIPAA) and the Health Information Trust Alliance (HITRUST). If you cannot deliver the necessary requirements or needs of the security market today, your client or potential customer will be forced to go elsewhere.
I recently attended a leading cybersecurity conference, and during a panel discussion with knowledgeable cyber professionals, a question was asked from the audience. The IT manager for a large municipality was concerned about the extensive number of cameras and door locks connected to his network. He explained that he wanted to understand what type of vulnerabilities this practice presented to his organization and what he could do to help protect them better.
It was a great question and the response was simply that he should work closely with his security system provider for guidance. If that is the case, are you prepared to have that discussion? Systems integrators need to be educated and ready to answer questions with tangible solutions. When you can have a knowledgeable conversation you will also provide better value to the organization and the ability to present a turnkey, full-service solution that not only addresses physical security but cyber threats and network protection.
What if your customer’s access control, video surveillance or mass notification system falls victim to ransomware? Do you have a plan in place with your customer, and are you taking proactive measures to alleviate the possibility? Are you making sure the equipment you provide is cyber-hardened and that you are deploying the necessary processes during system installation to further safeguard information residing on the network?
As system integrators, we must understand that the majority of our customers are looking for our expertise, and that we need to help guide them appropriately. Discussing the vulnerabilities that security system devices have on their network, along with cyber-attack risk such as ransomware should be part of the initial discussion in the pre-installation consultation phase.
That is also a differentiator for your business – and a necessary service for the physical security industry moving forward as billions of devices continue to be integrated and connected with the internet of Things (loT). End-users are not going to stop asking about cyber threats; instead, their inquiries and concerns will only escalate.
The Business Proposition
Systems integrators need to evolve their businesses from simply installing physical security detection. They need to understand and have a knowledgeable conversation with clients on additional safeguards, processes and best practices to help mitigate cyber threats and ransomware.
There are tangible steps that systems integrators can take to address ransomware and cybersecurity as they relate to physical security system deployment. They serve the multi-purpose of protecting the client, developing and furthering the integrator’s trusted provided status, and potentially providing new service and maintenance options that lead to RMR.
Here are eight insights to get started:
1. Get educated. PSA Security Network gets high marks for bringing the cybersecurity conversation to the table at its annual PSA TEC conference several years ago. The education raised awareness to the integrator community and has been followed by new committees for education and best practices (see more on page 30).
SIA education at ISC West 2017 had more than 10 sessions on cybersecurity. Professionals from the cyber world educated the systems integration industry by discussing cyber risks, illustrating how physical security systems can be breached, and providing guidance to improve the overall cyber posture of a networked system installation.
2. Consider third-party experts. With a massive shortage of cyber-trained experts in North America, the chances of your organization having one on staff is highly unlikely. Consider partnering with third-party cyber consultants and service providers. Bringing on this type of discipline within your company not only assists your customers, but also helps you develop policies and conduct assessments of your internal organization and its practices.
3. Secure yourself. Have you taken the appropriate steps to protect your organization by improving your own company’s cyber posture? Just like other companies, a ransomware attack on your organization can have a devastating impact, and a simple breach could put your customer and employee data at risk.
4. Install necessary backups. Having secure backup of On-Premise Physical Security Databases is paramount to protect against ransomware. There is an opportunity to assist your customers with deploying backup solutions as a managed service offering which may also present a new source of recurring monthly revenue (RMR). Once the service is in place, conduct regular testing of these backups to ensure that it can be restored fully.
5. Move to the cloud. Many of the cloud-based solutions today redundantly store system data and video automatically or on schedule. In addition, most cloud providers are held to an extremely high level of cybersecurity – with various levels of encryption and automatic disaster recovery.
Acceptance of cloud solutions by organizations is at an all-time high and manufacturers are releasing cloud solutions for numerous technologies. Take advantage of the opportunity to offer cloud solutions to your customers for inherent security and reliable network authentication.
6. Keep current with updates and patching. According to The United States Computer Readiness Team (US-CERT), systems that installed the MS17-010 patch were not vulnerable to WannaCry. According to experts, a lack of patching explains why institutions in China – where pirated software is more prevalent – were harder hit than in other parts of the world. Chinese state media said the ransomware struck nearly 40,000 institutions in that country, including government agencies, banks, schools and information technology firms.
“Unfortunately, many companies and organizations are slow, and in many cases, negligent on the update of patches that would prevent breaches,” says Chuck Brooks, VP of Government Relations and Marketing for Sutherland Government Solutions and Chairman of CompTIA’s New and Emerging Technology Committee.
For systems integrators, patching may represent a further RMR opportunity, as most end-users do not monitor manufacturer releases of device firmware updates or software patches. Providing this as a managed RMR service ensures safeguards that will not leave your customer vulnerable to attacks.
7. Develop incident response plans. Open the conversation with your customer about ransomware and cyber threats to physical security systems. Start with suggesting an incident response plan for these types of events and offer guidance in developing the physical security portion of the plan. Be the trusted expert and show them what steps you both can take if such an incident occurs.
8. Add RMR opportunities. Managed services that include backups, updates and cloud solutions provide great value to the customer and also yield tangible RMR. Properly developed and executed, these service offerings will separate you from your competition and build a better valuation for your company.
Rob Simopoulos is a Co-Founder of Defendify (www.defendify.io), which makes cybersecurity possible for small business through an all-in-one cybersecurity platform. In more than 20 years in the security industry, Simopoulos has been an entrepreneur, receiving numerous awards and recognition. He can be reached at [email protected], 888-508-9221 x 101.
Sidebar: Infection Protocol
Government-recommended steps to deal with a ransomware attack
The United States Computer Readiness Team (US-CERT) recommends that organizations consider taking the following steps upon an infection with ransomware:
• Isolate the infected computer immediately: Infected systems should be removed from the network as soon as possible to prevent ransomware from attacking network or share drives.
• Isolate or power-off affected devices that have not yet been completely corrupted: This may afford more time to clean and recover data, contain damage, and prevent worsening conditions. Protecting Your Networks from Ransomware
• Immediately secure backup data or systems by taking them offline: Ensure backups are free of malware.
• If available, collect and secure partial portions of the ransomed data that might exist.
• If possible, change all online account passwords and network passwords after removing the system from the network. Furthermore, change all system passwords once the malware is removed from the system.
• Delete Registry values and files to stop the program from loading.
• Implement your security incident response and business continuity plan: Ideally, organizations will ensure they have appropriate backups, so their response to an attack will simply be to restore the data from a known clean backup. Having a data backup can eliminate the need to pay a ransom to recover data.
• Contact law enforcement immediately: We strongly encourage you to contact a local field office of the Federal Bureau of Investigation (FBI) or U.S. Secret Service immediately upon discovery to report a ransomware event and request assistance. Law enforcement may be able to use legal authorities and tools that are unavailable to most organizations, as well as enlist the assistance of international partners to locate the stolen or encrypted data or identify the perpetrator. Law enforcement agencies and the Department of Homeland Security’s National Cybersecurity and Communications Integration Center can also assist organizations in implementing countermeasures and provide information and best practices for avoiding similar incidents in the future.
Paying the Ransom
There are serious risks to consider before paying the ransom. The U.S. government does not encourage paying a ransom to criminal actors; however, after systems have been compromised, whether to pay a ransom is a serious decision, requiring the evaluation of all options to protect shareholders, employees and customers. Victims will want to evaluate the technical feasibility, timeliness, and cost of restarting systems from backup.
Ransomware victims may also wish to consider the following factors:
• Paying a ransom does not guarantee an organization will regain access to their data; in fact, some individuals or organizations were never provided with decryption keys after paying a ransom.
• Some victims who paid the demand were targeted again by cyber actors.
• After paying the originally demanded ransom, some victims were asked to pay more to get the promised decryption key.
• Paying could inadvertently encourage this criminal business model.
Sidebar: Protect Yourself
Seven ransomware defense steps to communicate to end-users
The WannaCry ransomware attack was, in fact, largely preventable – if only more Windows users had installed the critical security patch that Microsoft released for it two months ago. “Criminals took advantage of the fact that most people still don’t do enough to protect their computers,” Marty P. Kamden, CMO of NordVPN (Virtual Private Network), said in a statement.
To raise public awareness about what end-users can do to protect themselves and the data held by organizations they work, here are seven best practices for ransomware protection:
1. Install latest security updates. Security updates often contain patches for latest vulnerabilities, which hackers are looking to exploit.
2. Do not open anything suspicious in email. Delete dubious emails from banks, ISPs, credit card companies, etc. Never click on any links or attachments in emails that you were not expecting, and never give out personal details if asked via email.
3. Back up all data. Use an alternate device and keep it unplugged and stored away. Backing up data regularly is the best form of ransomware protection, because only unique information is valuable.
4. Use a VPN for additional safety. Using a VPN when browsing can protect against malware that targets online access points –which is especially relevant when using a public hotspot. However, keep in mind that a VPN cannot protect someone from downloading malware. While a VPN encrypts online activity, users should be careful when downloading and opening certain files or links.
5. Close pop-up windows safely. Ransomware developers often use pop-up windows that warn of some kind of malware. Do not click on the window; instead, close it with a keyboard command or by clicking on the taskbar.
6. Use strong passwords and a password manager. Perhaps the most basic requirement for any online account setup is using strong passwords, and choosing different passwords for different accounts. Weak passwords make it simple for hackers to break into an account. A strong password has a minimum of 12 characters, and includes a strong mix of letters, numbers and characters. Since it is not easy for users to remember strong passwords for each site, use a password manager, such as truekey.com, LastPass or 1Password.
7. Use anti-virus programs. Make sure one of the latest reputable anti-virus programs is installed.
Infection Protocol
Government-recommended steps to deal with a ransomware attack
The United States Computer Readiness Team (US-CERT) recommends that organizations consider taking the following steps upon an infection with ransomware:
• Isolate the infected computer immediately: Infected systems should be removed from the network as soon as possible to prevent ransomware from attacking network or share drives.
• Isolate or power-off affected devices that have not yet been completely corrupted: This may afford more time to clean and recover data, contain damage, and prevent worsening conditions. Protecting Your Networks from Ransomware
• Immediately secure backup data or systems by taking them offline: Ensure backups are free of malware.
• If available, collect and secure partial portions of the ransomed data that might exist.
• If possible, change all online account passwords and network passwords after removing the system from the network. Furthermore, change all system passwords once the malware is removed from the system.
• Delete Registry values and files to stop the program from loading.
• Implement your security incident response and business continuity plan: Ideally, organizations will ensure they have appropriate backups, so their response to an attack will simply be to restore the data from a known clean backup. Having a data backup can eliminate the need to pay a ransom to recover data.
• Contact law enforcement immediately: We strongly encourage you to contact a local field office of the Federal Bureau of Investigation (FBI) or U.S. Secret Service immediately upon discovery to report a ransomware event and request assistance. Law enforcement may be able to use legal authorities and tools that are unavailable to most organizations, as well as enlist the assistance of international partners to locate the stolen or encrypted data or identify the perpetrator. Law enforcement agencies and the Department of Homeland Security’s National Cybersecurity and Communications Integration Center can also assist organizations in implementing countermeasures and provide information and best practices for avoiding similar incidents in the future.
Paying the Ransom
There are serious risks to consider before paying the ransom. The U.S. government does not encourage paying a ransom to criminal actors; however, after systems have been compromised, whether to pay a ransom is a serious decision, requiring the evaluation of all options to protect shareholders, employees and customers. Victims will want to evaluate the technical feasibility, timeliness, and cost of restarting systems from backup.
Ransomware victims may also wish to consider the following factors:
• Paying a ransom does not guarantee an organization will regain access to their data; in fact, some individuals or organizations were never provided with decryption keys after paying a ransom.
• Some victims who paid the demand were targeted again by cyber actors.
• After paying the originally demanded ransom, some victims were asked to pay more to get the promised decryption key.
• Paying could inadvertently encourage this criminal business model.
Protect Yourself
Seven ransomware defense steps to communicate to end-users
The WannaCry ransomware attack was, in fact, largely preventable – if only more Windows users had installed the critical security patch that Microsoft released for it two months ago. “Criminals took advantage of the fact that most people still don’t do enough to protect their computers,” Marty P. Kamden, CMO of NordVPN (Virtual Private Network), said in a statement.
To raise public awareness about what end-users can do to protect themselves and the data held by organizations they work, here are seven best practices for ransomware protection:
1. Install latest security updates. Security updates often contain patches for latest vulnerabilities, which hackers are looking to exploit.
2. Do not open anything suspicious in email. Delete dubious emails from banks, ISPs, credit card companies, etc. Never click on any links or attachments in emails that you were not expecting, and never give out personal details if asked via email.
3. Back up all data. Use an alternate device and keep it unplugged and stored away. Backing up data regularly is the best form of ransomware protection, because only unique information is valuable.
4. Use a VPN for additional safety. Using a VPN when browsing can protect against malware that targets online access points –which is especially relevant when using a public hotspot. However, keep in mind that a VPN cannot protect someone from downloading malware. While a VPN encrypts online activity, users should be careful when downloading and opening certain files or links.
5. Close pop-up windows safely. Ransomware developers often use pop-up windows that warn of some kind of malware. Do not click on the window; instead, close it with a keyboard command or by clicking on the taskbar.
6. Use strong passwords and a password manager. Perhaps the most basic requirement for any online account setup is using strong passwords, and choosing different passwords for different accounts. Weak passwords make it simple for hackers to break into an account. A strong password has a minimum of 12 characters, and includes a strong mix of letters, numbers and characters. Since it is not easy for users to remember strong passwords for each site, use a password manager, such as truekey.com, LastPass or 1Password.
7. Use anti-virus programs. Make sure one of the latest reputable anti-virus programs is installed.
About the Author

Rob Simopoulos
Rob Simopoulos is the Co-Founder of Defendify, the all-in-one cybersecurity platform that makes cybersecurity possible for Small Business. In his 20+ years in the security industry, he has received awards and recognition from many trusted industry experts and publications. Email him at [email protected].