Editor's Note: Time to Heed the Warnings
This article originally appeared in the June 2021 issue of Security Business magazine. When sharing, don’t forget to mention Security Business magazine on LinkedIn and @SecBusinessMag on Twitter.
As I was sitting in a gas line in the middle of May because a gas pipeline company employee probably clicked a phishing link in an email or network security practices were lax, it got me to thinking: The cybersecurity industry has been evangelizing the dangers of ransomware for quite a while; yet, we have seen the threat evolve quickly from holding some random person’s iTunes library for a quick payday into full-fledged terrorist-like attacks on critical infrastructure.
Furthermore, major enterprises all know that their own email users cannot be trusted even slightly to not fall victim to the most basic of email scams. And still, it seems the majority of these organizations are woefully unprepared for that eventuality.
Colonial Pipeline reportedly paid roughly 75 Bitcoin to buy back its vital files, stolen in the latest headline-grabbing ransomware attack (get the full story here). That’s nearly $5 million.
Where are the backups? I am a normal person – who, understandably, is more exposed to security issues than most – but when ransomware became “a thing,” I went out and bought a 2TB external hard drive, put all of my family photos and music library on it, and then stashed it nowhere near my computer or attached to any network.
Yes, updating my music library in three different places – hard drive, cloud and external hard drive – every time I add anything new is a pain, but it is a few extra minutes of effort that will turn out to be well worth it when some jerk wants to hold my files for ransom because my 9-year-old clicked a link in an email.
How is this not happening at the macro enterprise level? Maybe they aren’t considering the stakes. From Q4 2020 to the end of Q1 2021, the average ransomware payment increased 43% to $220,298, according to Coveware. Don’t forget, we are dealing with the bottom-feeder type of hacker groups where actually paying a ransom does not guarantee recovery of anything, nor does it protect from a second attack.
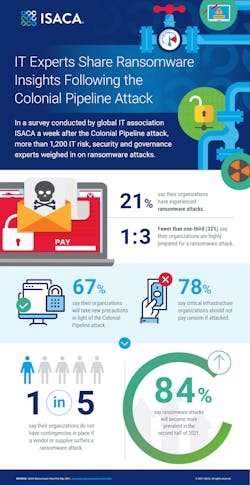
A survey right after the Colonial Pipeline incident by the Information Systems Audit and Control Association (see the graphic above) shows that just 32% of IT pros say their organization is highly prepared for a ransomware attack, and 67% say they plan to take new precautions.
Check out this month's "Insure Your Future" column to find out what has happened to cyber insurance premiums due to ransomware (hint, we used the term “skyrocketed”).
The lightbulb should have just turned on for security integrators. Ransomware hits every vertical. These people and organizations need you.
Paul Rothman is Editor-in-Chief of Security Business magazine. Email him your comments and questions at [email protected]. Access the current issue, full archives and apply for a free subscription at www.securitybusinessmag.com.
About the Author
Paul Rothman
Editor-in-Chief/Security Business
Paul Rothman is Editor-in-Chief of Security Business magazine (www.securitybusinessmag.com) and has been covering the security industry for various outlets since 2001. Email him your comments and questions at [email protected].