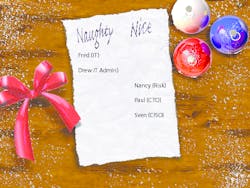
Cybersecurity's naughty and nice list
The past year was another challenging one for IT security, in which cyberattacks continued to increase in frequency and severity. As we welcome 2016, it’s a good time to reevaluate the IT security practices that have been working, and those that haven’t. What habits from the past year would land your organization on cybersecurity’s naughty list and which would land you on the nice list?
It’s amazing how kids always know what list they’ve been on, and somehow tend to become “nicer” as the holidays near. Unfortunately, IT security pros usually can’t change that quickly, but there is good news. If you’ve been naughty for one reason or another, the New Year is a good time to implement change. Here’s a quick list of common habits that will help you figure out just how naughty you’ve been, and what you might have to do to redeem yourself in the New Year.
Assuming You’re Not a Target vs. Assuming You’ve Already Been Breached
Shockingly, recent research from the Ponemon Institute found that half of IT security practitioners in the U.S. view their organization as an unlikely target for attack. If today’s headlines are any indication, any organization that stores its data or customers’ data can become the target of a damaging data breach. Assuming you’re not a target can lead to reduced diligence in defending against and detecting advanced threat activity and land you on the naughty list for sure.
To get on the nice list, you have to assume the “bad guys” have already made their way into your network. Historically, building higher walls and deeper moats kept bad actors at bay, but for today’s attacks, organizations will first need to assume they’ve been breached, and then analyze the common characteristics of intrusions to detect threats early—before significant damage is done.
Focusing Only on Known Threats vs. Utilizing Advanced Threat Detection to Look for New Threats
Organizations are asking for trouble if they assume traditional approaches to security will keep them safe from an attack. Protecting only against “known” threats such as malware, and known vectors such as email and web browsing, is proving inadequate to combat today’s advanced cybercriminals, who are continuously identifying new ways to infiltrate systems unnoticed.
But if your organization is using advanced detection methods that could also identify new, unknown threats, it’s in a much safer place. One example of this is using machine learning technology that can baseline normal activity. This type of technology can analyze millions of data points each minute to identify and flag anomalous activity. This not only helps detect known threats, but also identifies unusual behaviors that may be associated with advanced threat activity and unknown threats. This is particularly critical as hackers adopt new attack methods.
Ignoring vs. Embracing the Internet of Things
If you’ve only been monitoring desktops, laptops and servers, you’re going to find a lump of coal in your stocking. Assuming that only computing devices represent risks to an organization’s data and systems creates major security gaps. Printers, scanners, POS systems, mobile devices, HVAC systems, and even drones can be exploited to enable an attacker to gain access to a network.
Organizations that are serious about defending their IT infrastructure know they first need to understand the potential attack surface. This means monitoring anything with an IP address. Taking a bottoms-up approach by cataloging, classifying, and controlling each IP address on the network is a sound approach to reducing the likelihood of surprise attack vectors.
Getting Lazy with Layered Security vs. Fortifying Each Layer Individually
Conventional security wisdom has held that multiple layers of defense are part of a sound security posture. However, unless diligently managed, reliance on the existence of a “backup plan” in the form of multiple layers of defense could actually backfire. Too often organizations fail to apply proper diligence to each layer. Assuming that “one of the other layers will stop it” is dangerous and definitely a naughty practice.
Acting as if each layer is the only layer is a nice and much safer practice. Organizations investigating a data breach often find that attackers have gained access to their networks by taking advantage of weaknesses in multiple layers of defense. To protect against human error, organizations should organize security teams into logical groups, where each group has responsibility for only one layer of the security architecture, and each should operate as if there were no other layers present.
Wasting SIEM Data vs. Extracting its Hidden Value
Wherever IT log data is aggregated, whether in Splunk, Elastic, Hadoop, or traditional SIEM, the vast majority of the data “lake” is not fully analyzed until it’s too late, and the forensic team has been called.
Organizations that rely only on SIEM correlation rules to analyze their data are essentially letting all this potentially valuable data “evaporate” before it can be used.
Augmenting SIEM and other data aggregation tools with advanced analytics give them a bigger “brain” that’s capable of continually analyzing IT log data. This can return actionable insights from data that might have otherwise “evaporated” before it could be used.
Working Harder vs. Working Smarter
Companies that have been relying more and more on human effort to detect attacks are definitely on the naughty list. Adding another dozen analysts to a security operations center just won’t get the job done. This approach requires that security teams anticipate every possible move a hacker might make. Unfortunately, the human brain simply can’t keep track of all the possible indicators of advanced threat activity. Without the capacity to automate the analysis of huge volumes of infrastructure log data, costs will rise, and potential threats will go unnoticed.
On the other hand, those that are adopting technology such as behavioral analytics to help their existing teams work smarter make the nice list. Using a technology like unsupervised machine learning as “algorithmic assistants,” organizations can automate detection of advanced threat activity without the manual effort needed to write rules, create thresholds and check reports. Even an army of security analysts would be unable to accomplish what this advanced technology can do to detect unusual activity associated with advanced threats.
About the Author:
Mike Paquette has more than 30 years of technology product development experience, including executive roles with several startups in the areas of consumer apps, mobile app ecosystems, and Security Information and Event Management (SIEM). He’s currently VP of products at Prelert, a company that provides behavioral analytics for IT security and operations teams.